
E-COMMERCE: EVER MORE DIFFICULT TO IDENTIFY COUNTERFEIT OR PIRATE GOODS
E-commerce between lights and shadows. While it is true that the health emergency associated with the pandemic has cleared customs clearance for online shopping in all its forms, it is also true that the very nature of marketplaces has made and makes it difficult for users to distinguish counterfeit and pirated goods from authentic and legal ones.
FIND OUT HOW VERICODE CERTIFIES THE AUTHENTICITY OF PRODUCTS SOLD ONLINE
The indicators of off-line illegality
In past years, counterfeit and pirated goods have been sold on street corners, less traveled alleys or more borderline markets. Those who go to these places are generally able to discern the risk of buying an illegitimate asset by relying on red flag indicators, such as:
- a suspicious position of the seller
- poor quality packaging
- goods suddenly pulled out of the trunks of cars and pickup trucks
- far too discounted prices
E-commerce: that aura of authenticity so misleading
On e-commerce platforms, however, consumers are unknowingly exposed to counterfeit and pirated goods in environments and conditions that make the items appear authentic. Marketplaces, in particular, provide an aura of authenticity and trust, mimicking the look and feel of serious portals. These online marketplaces do not contain the same red flag indicators as offline ones: not only is the seller's true location often unknown or obfuscated, but images of the item and packaging of the authentic product can be used. In this way the illegitimate good can be exchanged for the original one, both in the logistics center of the platform and on the e-commerce platform itself through the use of the same product identifier for both the authentic and the counterfeit good.
Beware of social channels
Vendors of counterfeit and pirated products have also recently taken advantage of social media and messaging websites or mobile apps to subvert detection controls and fool consumers. A quick, easy, inexpensive and common tactic is to create an account on social media platforms and use targeted advertising posts or campaigns to advertise counterfeit or pirated goods, from both the black and gray markets. Posts and advertisements convey authenticity as they often contain the same images, hashtags and keywords used by the brand, which contributes to consumer confusion. The advertisements direct consumers to ecommerce websites designed to evade detection or ask consumers to communicate via a messaging app for details on how to purchase the authentic look
counterfeit or pirated merchandise. Ads and messages often hide the unscrupulous nature of the transaction by claiming to be an exclusive wholesale or bulk purchase. An online payment service, typically connected or affiliated with the social media or messaging platform, allows the immediate and secure completion of the transaction.
E-commerce and inauthentic products: some examples.
Another tactic that is gaining popularity on social media and other platforms, such as image hosting platforms, are so-called hidden links. With a hidden linking scheme, a seller will advertise a seemingly original product but direct a potential customer to purchase a different (counterfeit) product on an e-commerce site. For example, a hidden link ad for a famous brand's shoe might link to a page on a well-known e-commerce platform that offers generic socks for sale. The hidden link ad directs the buyer to provide a code, color, or other identifier to signal the seller to send the counterfeit shoes instead of the socks. The hidden link ad can also instruct the buyer not to ask questions or leave reviews on the ecommerce platform. This treacherous process is designed to evade the counterfeit detection systems of e-commerce providers.
E-commerce: checks and controls on social networks are scarce
There are many brands expressing concern that many social media providers do not verify or check the identity of advertisers and their pages to prevent the accounts of repeat offenders. Rights holders encourage social media providers to provide advanced anti-counterfeiting tools, programs and procedures to help combat these subversive counterfeiting methods.
E-commerce: logistics is the weakest link in the supply chain
Products sold in brick-and-mortar stores are often shipped in bulk containers and then distributed nationwide via traditional train and truck networks. The methods for detecting counterfeits in these bulk containers at the port of entry are well established and effective. Unlike the use of bulk cargo for products sold in physical stores, products sold on e-commerce platforms, including counterfeit products, are shipped directly to the consumer using small packages. The International Chamber of Commerce found that counterfeiters use international air parcels because the high volume of these parcels makes it more difficult to guard the content.
The granularization of shipments difficult to control
A recent OECD report points out that distributing counterfeit products on a series of small packages spreads the risk of detection and reduces the loss resulting from the seizure of one or more shipments, suggesting that losses to the counterfeiter on an ongoing basis would be within a tolerable range.
The OECD report also explains how difficult it is for authorities to detect counterfeits in small packages compared to containers, as the latter provide customs officials with more information that can help identify counterfeit shipments. Furthermore, the effort required by law enforcement to seize a shipment does not vary according to the size of the shipment, which means that seizing a package of a few counterfeit goods requires the same resources as seizing a container with hundreds of infringing goods.
Defending intellectual property and consumers
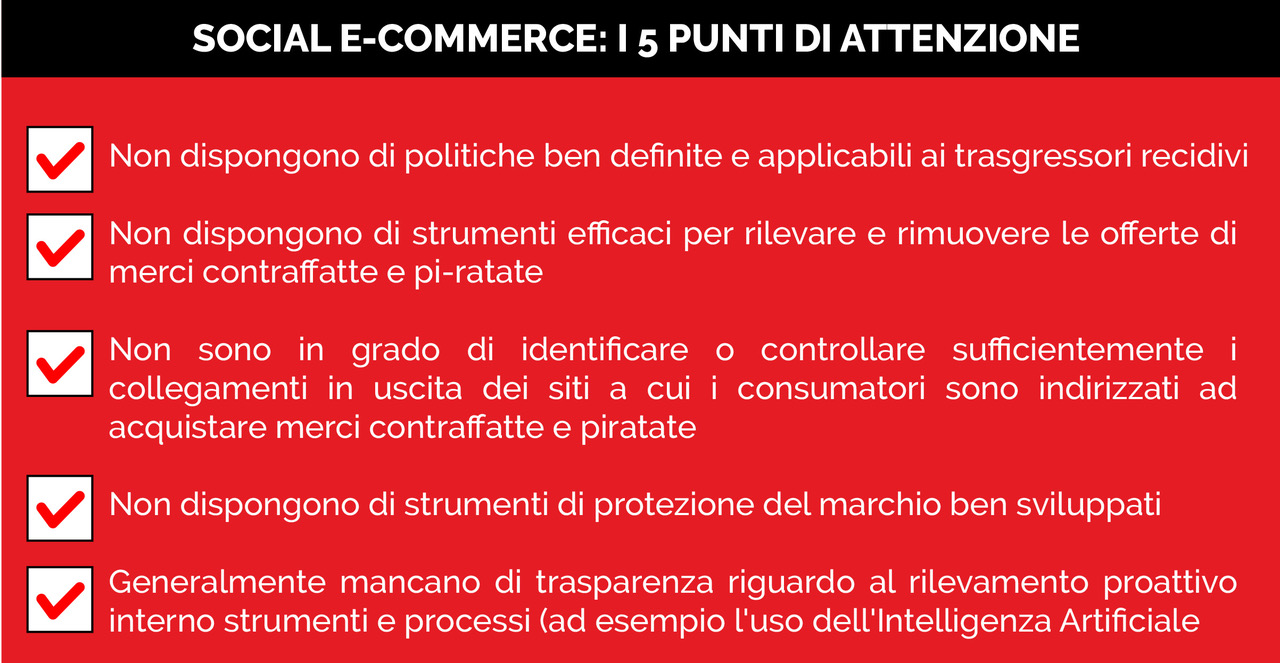
The complex ecosystem of e-commerce includes various elements such as registers, domain names, reverse proxy services, hosting providers, caching services, advertisers, ads, payment solutions, social media platforms and search engines. The holders of production and distribution rights point out that social media platforms do not have the anti-counterfeiting policies, processes and tools that are becoming common on many e-commerce platforms such as, for example, effective notification and takedown procedures, filters and proactive anti-counterfeiting tools and strong policies against repeat offenders. Social media platforms can adopt strong and effective intellectual property enforcement policies, increasing transparency and collaboration with rights holders to quickly address complaint handling and working more closely with law enforcement to identify violation of IP (Intellectual Property). Also to avoid repercussions on brand reputation and brand awareness
Tracking, tracing and authentication technologies
Manufacturing and distribution brands should adopt a more functional, transparent and securitized goods handling model. In this sense, there are many technologies to support the supply chains: from AutoID through the use of one-dimensional and two-dimensional codes up to the use of smart labels which, thanks to a unique identification code, allow to guarantee the quality of the information shared. along all the manufacturing processes of the supply chains: from the arrival of raw materials to all intermediate stages of production, up to including the arrival of goods on the shelves. To make the difference in e-commerce today there are state-of-the-art solutions that also help end consumers to have access to information that guarantee the authenticity of a product even before purchasing it!
- Log in to post comments